Why Law Firms Need Managed IT Support More Than Ever
04/23/26
Your client’s deposition is tomorrow. Your document management system just went down. Your IT guy – a freelancer you call when things break – isn’t picking up the phone. This is not a hypothetical. It happens at small and mid-sized law firms every week. And in a field where missed deadlines have real legal consequences, […]
Your IT Company Should Pick Up the Phone
04/22/26
When something breaks, the problem is rarely just technical. A proposal is due in two hours. Your accounting system crashes. Your team is blocked. You call IT and get a voicemail, a ticket number, and an auto-reply saying someone will follow up within one business day. That is the moment you realize your IT support […]
Managed IT Support Should Help Right Away, Not Add Another Delay
04/10/26
You call for managed IT support because something is broken, blocked, or slowing your team down. Maybe a user cannot get into email. Maybe a line-of-business app has stopped working. Maybe a security issue needs attention now. What you do not need in that moment is a long intake process, a handoff to someone else, […]
DarkSword Leaked: What Every iPhone User Needs to Do Right Now
03/26/26
If you have an iPhone, this matters to you. On March 23, 2026, a sophisticated iPhone hacking toolkit known as DarkSword was leaked publicly on GitHub, meaning a tool once reserved for government intelligence agencies and elite cyber-espionage operations is now freely available to any hacker on the planet. Security experts are calling it one […]
Bad Actors Aren’t Waiting. Is Your Business Ready for a Cyberattack?
02/25/26
You don’t have to be a Fortune 500 company to get hit by a cyberattack. In fact, small and mid-sized businesses are targeted more often than large enterprises, precisely because attackers assume your defenses are weaker. If you’ve never seriously asked whether your business is ready for a cyberattack, that gap in thinking is exactly […]
The Real Reason You’re Looking for a New IT Company
01/02/26
You’re not searching for a new IT provider because your tickets take too long to close. You’re not doing it because the bill went up again, or because you had to call three times before someone picked up. Those things are real, and they matter. But they’re not actually why you’re making the call. After […]
Is Your Business Actually Using AI, or Just Watching Everyone Else Get Ahead?
12/19/25
You’ve heard it at every conference, in every newsletter, from every vendor trying to sell you something: AI is going to change everything. And they’re right. The frustrating part is that most business owners nod along and then go back to doing exactly what they were doing before. Not because they don’t care. Because nobody has shown them a practical path […]
Your IT Shouldn’t Live in Someone Else’s Head
11/19/25
For businesses in New York City, Westchester, and Connecticut, one of the most overlooked risks in an IT relationship isn’t a cyberattack or a hardware failure, it’s a lack of visibility into your own environment. Think about how much critical IT knowledge lives inside your current IT provider’s systems, or worse, in the head of […]
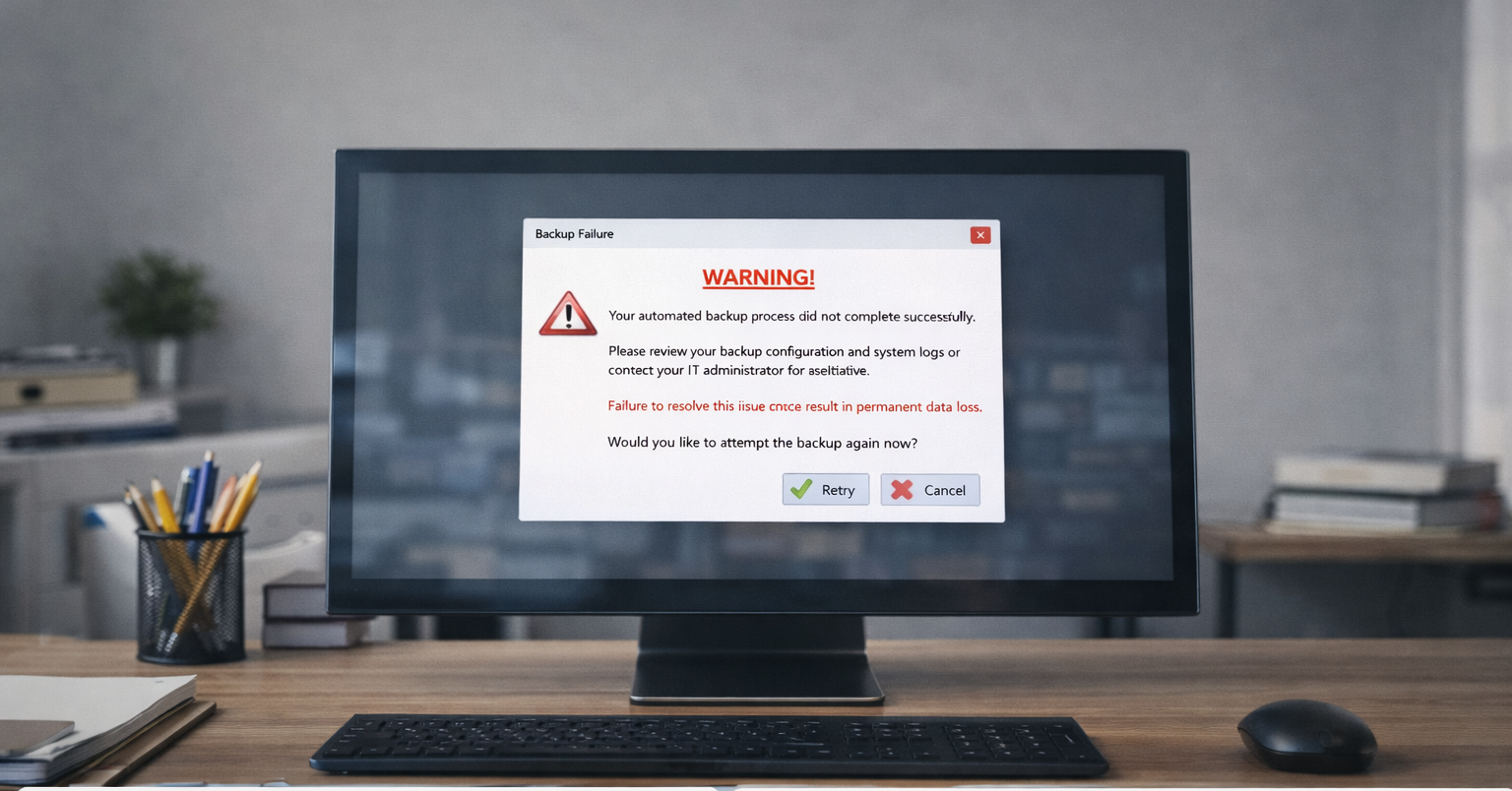
Your Backups Are Probably Broken. Here’s How to Find Out.
10/19/25
For businesses in New York City, Westchester, and Connecticut, data backup is one of those IT topics everyone assumes is handled until it isn’t. Here’s the question we ask every new client, and almost none of them can answer confidently: “If your entire server went down right now, how long would it take to recover […]